Last week I have implemented an Azure PoC at a customer site and was faced with the configuration of the S2S VPN tunnel between Azure and the on-premises site. You can check on the MSDN website which VPN devices are supported.
-> http://msdn.microsoft.com/en-us/library/azure/jj156075.aspx
The customer is using a FortiGate as VPN device and as you can see on the MSDN website you are forwarded to the FortiNet website. But I will provide you with the direct links to the documentation and the video on how to setup the S2S VPN tunnel to Azure.
-> http://docs.fortinet.com/d/fortigate-configuring-ipsec-vpn-between-a-fortigate-and-microsoft-azure
-> http://docs.fortinet.com/d/fortigate-video-ipsec-vpn-between-a-fortigate-and-microsoft-azure
I followed the steps in both how-to manuals, but the connection did not establish successfully afterwards. I went back to the MSDN website to check the IPsec parameters.
-> http://msdn.microsoft.com/en-us/library/azure/jj156075.aspx#bkmk_IPsecParameters
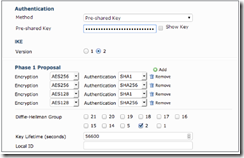
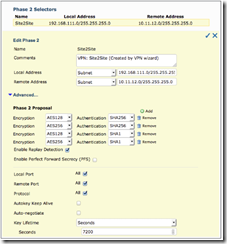
Comparing the configuration steps and the IPsec parameters I have found some differences. So I used the IPsec parameters provided by Microsoft instead of the parameters in the how-to manuals and the connection was established. I will show you now where you have to use the parameters provided by Microsoft.
Use as key lifetime 28800 seconds instead of 56600.
If you specify the settings for local address & remote address and they will not work try 0.0.0.0/0 for both. In the video PFS is enabled with the wrong Diffie-Hellman Group instead of 2 it should be 1. In the document PFS is not enabled, but you should. Then I have set the key lifetime to 3600 seconds instead of 7200. Additionally you can enable the autokey keep alive functionality.
I am not saying that the how-to manuals are wrong or not working. Only in my case that I had at a customer site they did not work.